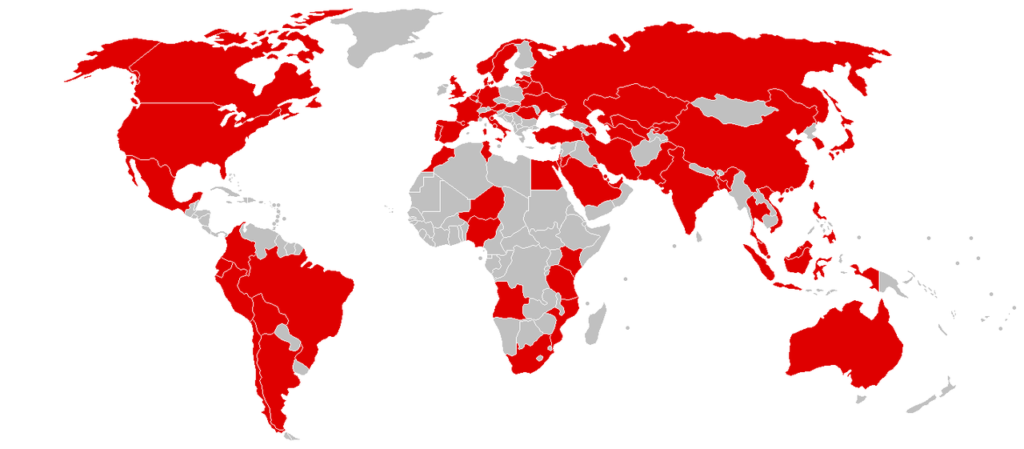
IT services around the world are waking up to the aftermath of the ‘Wannacry’ ransomware malware which hit a majority of countries around the world in such a short amount of time.
IT services across the private and public sectors of most countries have been working over the weekend to upgrade IT infrastructure and applying up to date patches to deal with the vulnerability that this malware exploits. For some, the weekend was enough to update all systems but there will be cases where there will be disruption to IT services as works are completed and systems brought back online. The impact of the attack on Australian businesses has been limited thus far, but the situation may change as time progresses.
As staff return to work today the general consensus is for all computer systems to be updated with the latest Windows patch – which was released by Microsoft over the weekend. IT services around the country and worldwide are on high alert and are working around the clock to pick up the pieces as well as fully protect systems from such an attacking penetrating their defences.
What we have learnt since the first infection on May 12th?
IT services firms have discovered that a Microsoft Windows Update back in March 2017 thwarted the initial version of the ‘Wannacry’ attack. This update took care of that attack. However, for many reasons from lack of resources to a desire to fully test new updates before pushing them out more widely, organisations are often slow to install such security updates on a wide scale. The cyber criminals took advantage of that and unleashed a similar ransomware infection a few days ago, which has lead to it having much more success. But as with most ransomware, ‘Wannacry’ seems short-lived and it is reported that once you have updated to the latest patch, the system will be protected from the ‘Wannacry’ ransomware.
But there is talk of another attack just around the corner.
Unfortunately with no specific details. But the IT services sector isn’t ruling out something like this from occurring again. This attack is lucrative and from an individual point of view, the ransom of $300 doesn’t sound like a huge amount to be held ransom for and some people will go ahead and pay up – with no assurance of getting their files back/unlocked. We may see various forms of the ‘Wannacry’ ransomware come to public light by freelancers or those who just want a shot at making a quick buck. Taking into account that a ‘kill switch’ helped stop the spread of ‘Wannacry’, potential attackers may get rid of a kill switch. Because the attack was so simple and unsophisticated, the IT services sector believed that the people or person involved were more along the lines of amateur, despite carrying out a relatively successful attack.
Once ransomware has encrypted your files there’s not a lot you can do. If you have a backup of the files you should be able to restore them after cleaning the computer, but if not your files could be gone for good. Some badly designed ransomware, however, has been itself hacked by security researchers, allowing recovery of data. But such situations are rare, and tend not to apply in the case of widescale professional hits like the Wannacry attack.
Ironically, a day before the attack went public, Donald Trump pushed for organisations to buy more modernised IT services. “Effective immediately, it is the policy of the executive branch to build and maintain a modern, secure, and more resilient executive branch IT architecture,” the order says. Here in Australia, Cyber Security Minister Dan Tehan says there have only been reports of three Australian businesses who have been impacted. “At this stage, it does seem like that we have missed the major impact of this ransomware incident,” he said. “We haven’t seen the like of this before but ransomware is occurring here in Australia.”
IntelliTeK is one of the fastest growing IT service providers that you will find on any list of managed service providers in Australia. We are always up to date with the latest threats to emails and IT security which is why we only partner with the best in the industry. If your company isn’t fully equipped to fend off cyber criminals, then get in touch with us so we can discuss your options. Call us on 1300 768 779, email us at info@intellitek.com.au, fill out the web form, or have a Live Chat with us below.