Watering hole attacks attempt to infect more than 100 organisations in 31 different countries in a new wave of attacks which has been underway since at least October 2016.
The attackers used compromised websites or “watering holes” to infect pre-selected targets with previously unknown malware. There has been no evidence found yet that funds have been stolen from any infected banks. First light of such attacks came when a bank in Poland discovered that is had unknown malware running on its computer systems. They then shared indicators of compromise (IOC) with other banks and many banks confirmed that they too had similar indicators of compromise.
The source of the attack appears to have been the Polish financial regulator website, which redirects visitors to an exploit kit which attempts to install malware on selected targets. There have been blocks attempts to infect customers in Poland, Mexico and Uruguay by the same exploit kit that infected the Polish banks. Since October, 14 attacks against computers in Mexico were blocked, 11 against computers in Uruguay, and two against computers in Poland.
The redirects appear to only be configured to only infect visitors from approx. 150 different IP addresses, and those 150 IP addresses belong to 104 different organisations within 31 different countries. The vast majority of these organizations are banks, with a small number of telecoms and internet firms also on the list.
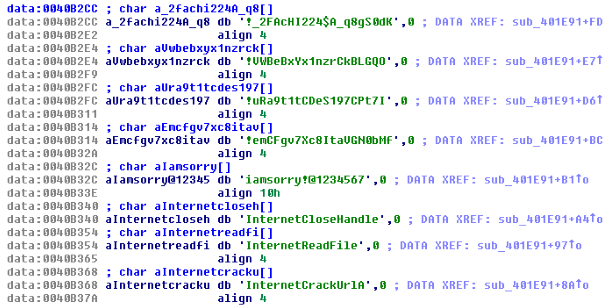
The malware used in the attacks (Downloader.Ratankba) was previously unidentified, although it was detected by Symantec under generic detection signatures, which are designed to block any files seen to engage in malicious activities. Analysis of the malware is still underway. Some code strings seen in the malware used shares commonalities with code from malware used by the threat group known as Lazarus.
Ratankba was observed contacting eye-watch[.]in for command and control (C&C) communications. Ratankba was then observed downloading a Hacktool. This Hacktool shows distinctive characteristics shared with malware previously associated with Lazarus. Lazarus has been linked to a string of aggressive attacks since 2009, largely focused on targets in the US and South Korea. Lazarus has been involved in high level financial attacks before and some of the tools used in the Bangladesh bank heist shared code similarities with malware used in historic attacks linked to the group.
Further investigation of these attacks is underway and, over time, more evidence may emerge about the identity and motives of the attackers. After a series of high profile attacks on banks during 2016, this latest incident provides a timely reminder of the growing range of threats facing financial institutions.